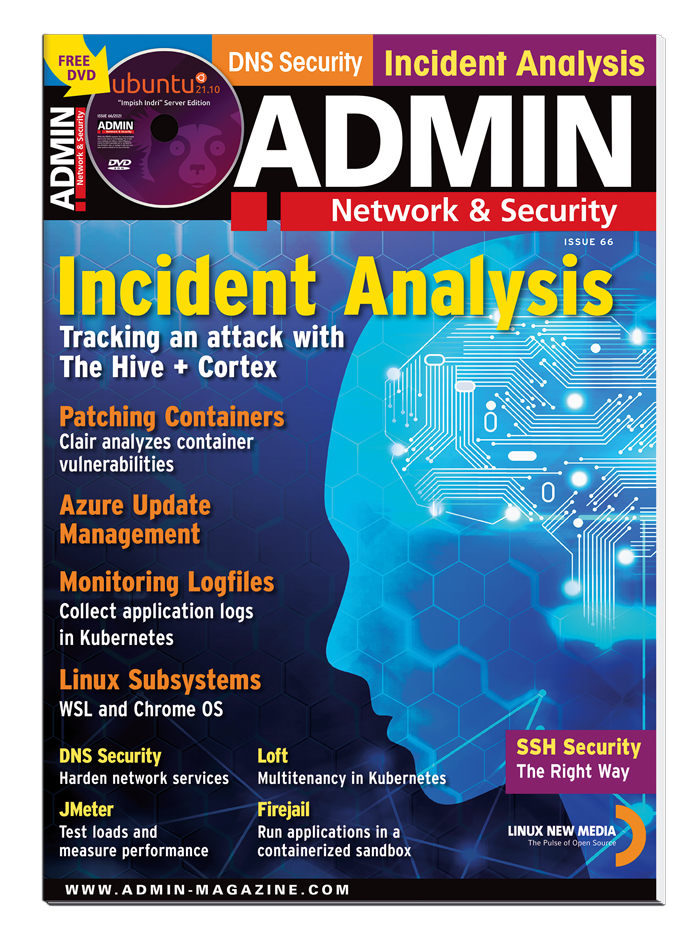
ADMIN #66 - Digital Issue
We look at updating, patching, and log monitoring container apps and explore The Hive + Cortex optimization.
DVD contents are not available with the digital edition.
Digital issues will be available once payment is confirmed.